|
Solution To Password Problems : GATE [ Graphic Access Tabular Entry ] An Interception-resistant Authentication System By Ni , Min [ Frank ] of GATE Cyber Technology, Atlanta GA USA, 2020 |
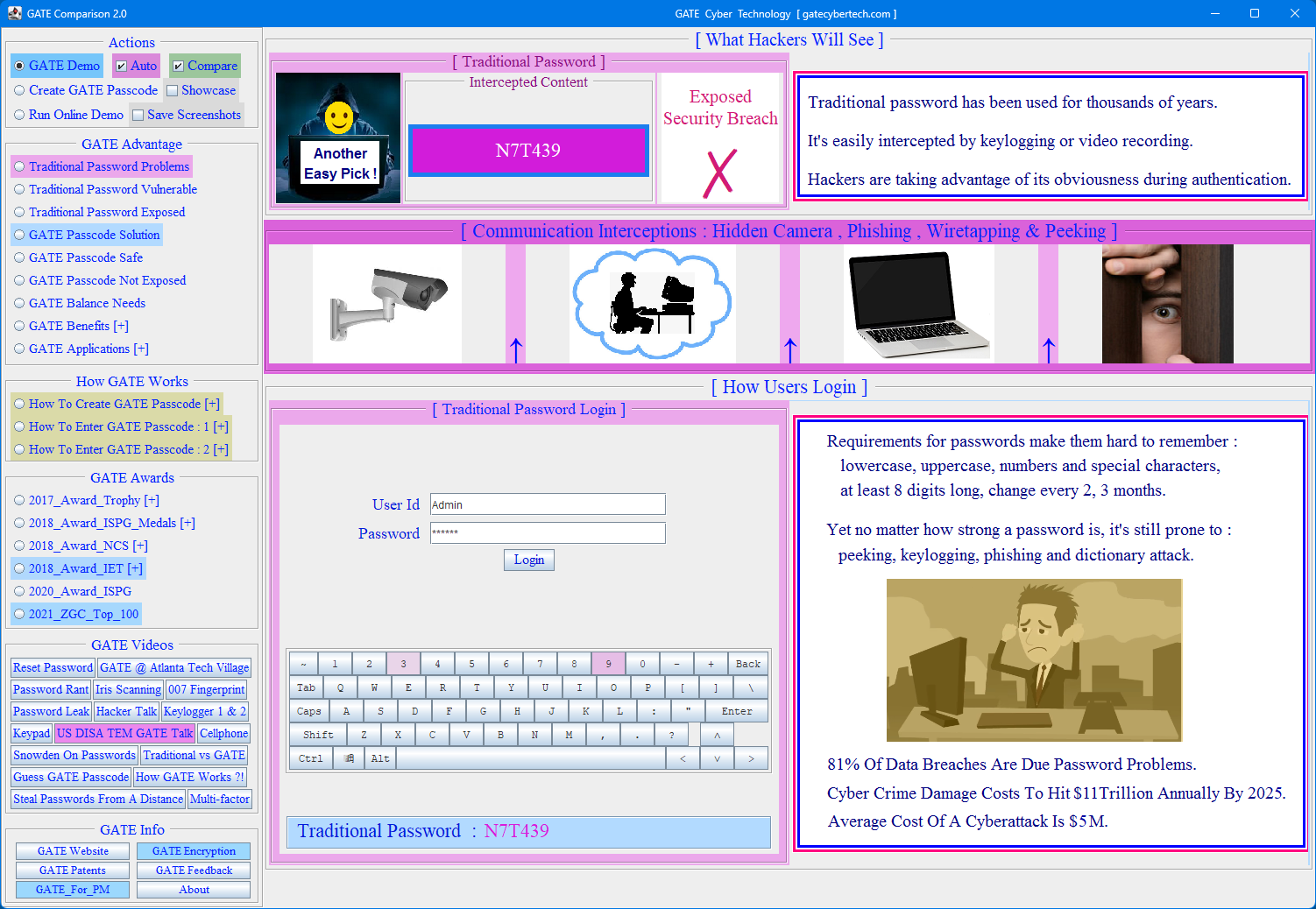
| GATE_Comparison |
|
GATE is a revolutionary password/passcode entry process that retains account security even in situations where potential intruders witness the entries being made. Based on user password choice, server renders password entry buttons/tokens on a screen, rendering multiple characters per button.
When button selection is made by a user there is no way for an observer to know the actual password due to the multiple characters per button. This makes GATE an interception-resistant authentication system which increases passcode strength exponentially.
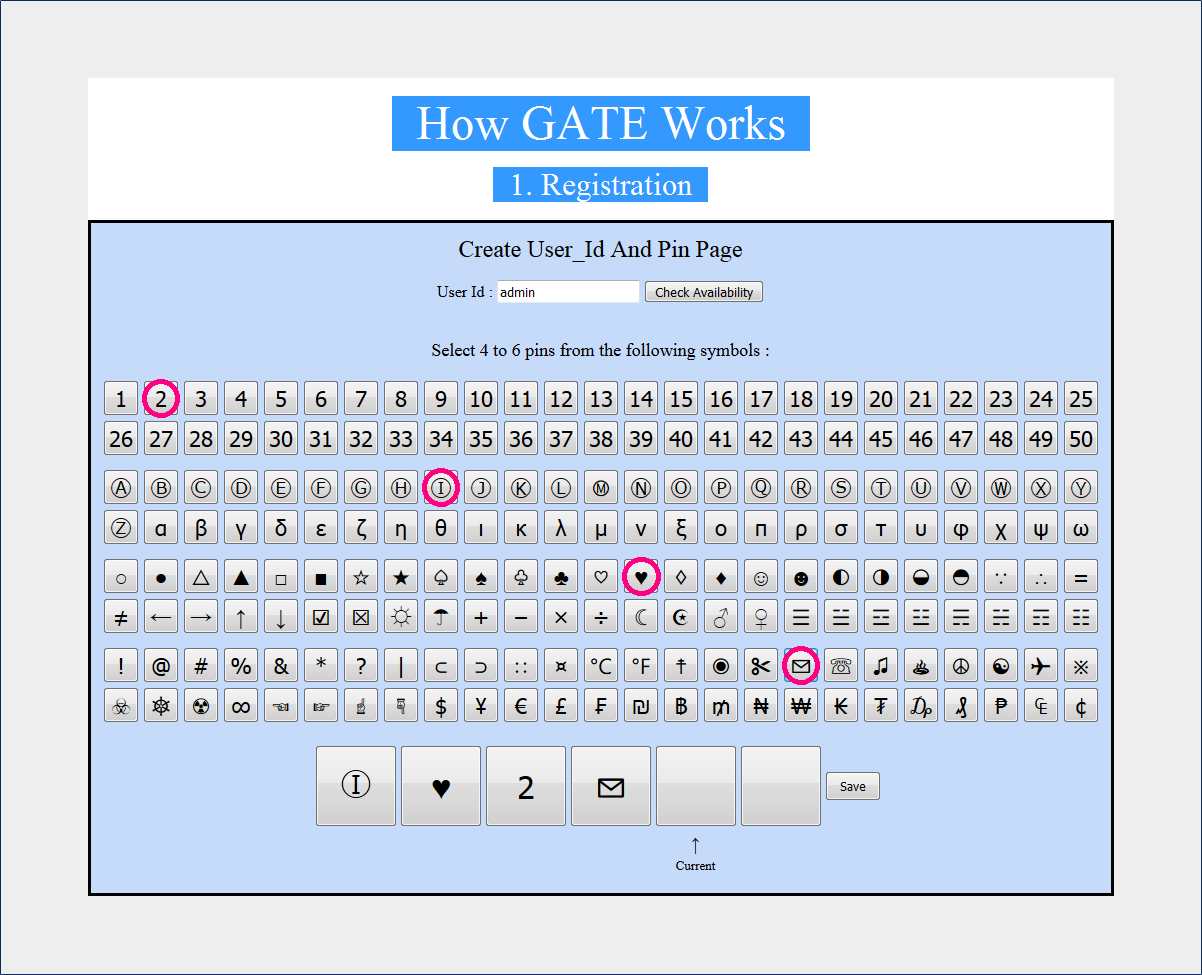
Each subsequent rendering of buttons by the server will be unique, based on the GATE algorithm, ensuring button selection cannot simply be repeated based on button location in order to infiltrate an account. Due to the rendering process required in order to present password buttons to a user, a server has to already know the password of the user in order to render an appropriate array of buttons. Therefore bogus or malicious servers will not be able to render an appropriate array of buttons to a user, which allows the user to recognize whether or not the screen he is looking at is being controlled by the appropriate body. In traditional password system, server authenticates user, yet with GATE, user also authenticates server, therefore defeat phishing by design. GATE can use short and easy to remember passcodes to defeat peeking, wiretapping, keylogging, phishing and dictionary attack without the restrictions of lowercase, uppercase, numbers & special characters ! Fixed passwords have the advantage of easy to remember, one time passwords have the advantage of hard to hack, GATE passcode is a fixed passcode to the user, but from the hackers' perspective, it changes every time, GATE passcodes have the best of both worlds, short [ 4 to 6 digit ] and easy to remember, yet secure and hard to hack.
Times have changed, we are now in the 21-century, yet we're still using the age old password system, hackers now have state-of-the-art tools to steal our passwords, we also need better ways to protect ourselves, we need to be a few steps ahead of the hackers. The fact that accounts with traditional passwords will be hacked is a matter of "when" not "if", they are just one hidden camera/keylogger/phishing attempt away from being compromised. Let's wake up to the cruel reality, rather than pretending not to see it by playing ostrich, hackers will see what you don't want to see [ weakness in traditional passwords ] and take advantage of it, a chain is only as strong as its weakest link ! Let's face it and fix this weak link ! Password managers only solve part of the password problem [ too many passwords to remember ], but leave the other important part unsolved [ user pin exposure during login : peek over the shoulder / keylogger / video camera ], if you rely on password managers for first part of the problem, they might come back and bite you big time for the 2nd part of the problem, because once your master password is exposed [ by keylogger / hidden camera ], all your passwords will be stolen. Hackers will enjoy the benefits password managers bring them, instead of having to hack dozens of your accounts, with the help of password managers, they now only need to hack just ONE ACCOUNT to get the master password and all your other accounts will be compromised.
As of July 2020, there are 15 Billion Credentials Currently Up for Grabs on Hacker Forums. World population is now 7.8 Billion, if you take out half of it from poor countries that don't have a lot of computers, there will be around 4 Billion left in developed countries with computers and online accounts, so that means averagely speaking, we all have 3 or 4 accounts breached ! In this video you can see how hackers intercepted user passwords from far away, which seems like a safe distance from the user, yet the hackers were able to figure out user passwords by looking at their finger movements and analyze the data to steal the passwords. GATE_Comparison is a FREE demo app to compare the weaknesses of traditional password systems to the strengths of the innovative GATE authentication system. You can learn How GATE Works before using GATE_Comparison. More GATE info is here and there.
GATE_Comparison app serves as a proof of concept, anyone interested in the interception-resistant GATE authentication system can contact me for a customized license.
|
| ||||
 | ||||
|
After download, please follow the instructions in the "Readme.txt" file to get started. GATE_Comparison is packaged with its own Java [ OpenJDK ], so even if user doesn't have Java already installed on his PC, the program will still work. It should work on all 64 bit Windows systems.
|
||||
 | ||||
 | ||||
 | ||||
 | ||||
 | ||||
GATE Cyber Technology
